Latest | Server installation and setup | Install the server | Introduction
Was this page helpful?
On this page
Introduction to the server installation
The server installation section describes a single-node SonarQube instance from the ZIP file or from the Docker image. For a Kubernetes installation, see Deploy SonarQube on Kubernetes. For details on clustered setup, see Install the server as a cluster.
Installation roadmap
Proceed as follows to install SonarQube on server side:
- Install the SonarQube database.
- Install the SonarQube server and perform a basic setup. You can install the server either from the ZIP file or from the Docker image.
- If necessary, perform advanced setup.
Instance components
A SonarQube instance comprises three components:
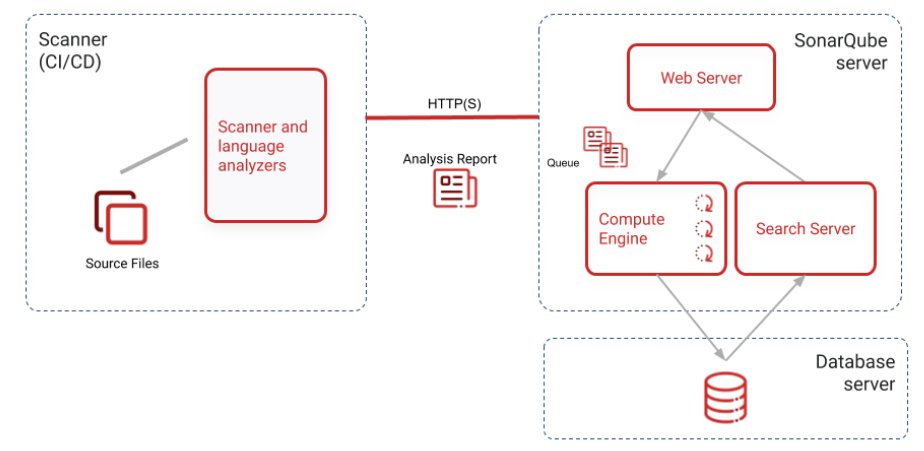
- The SonarQube server running the following processes:
- A web server that serves the SonarQube user interface.
- A search server based on Elasticsearch.
- The compute engine in charge of processing code analysis reports and saving them in the SonarQube database.
- The database to store the following:
- Metrics and issues for code quality and security generated during code scans.
- The SonarQube instance configuration.
- One or more scanners running on your build or continuous integration servers to analyze projects.
Hosts and locations
For optimal performance, the SonarQube server and database should be installed on separate hosts, and the server host should be dedicated. The server and database hosts should be located on the same network.
All hosts must be time-synchronized.